Last year, we covered the first known Rowhammer attack on GPUs, dubbed "GPUHammer," which proved that VRAM is also susceptible to bit flips. At the time, our story focused on how GPUHammer can cripple an AI model's accuracy from 80% to just 0.1% in an RTX A6000 with a single bit flip. Since then, two new Rowhammer attacks have surfaced that can gain root access to the CPU through your GPU, potentially compromising your entire system (story via Ars Technica).
These attacks are called "GDDRHammer" and "GeForge," as listed on the gddr.fail website. They both work quite similarly and share an identical end goal. But first, it's important to understand what Rowhammer is. Back in 2014, it was discovered that by constantly accessing rows of memory, you can induce a bit flip on purpose on neighboring rows. Since bits are stored as electrical charge, "hammering" them causes electrical interference that can flip 0s into 1s, or vice versa.
Article continues below
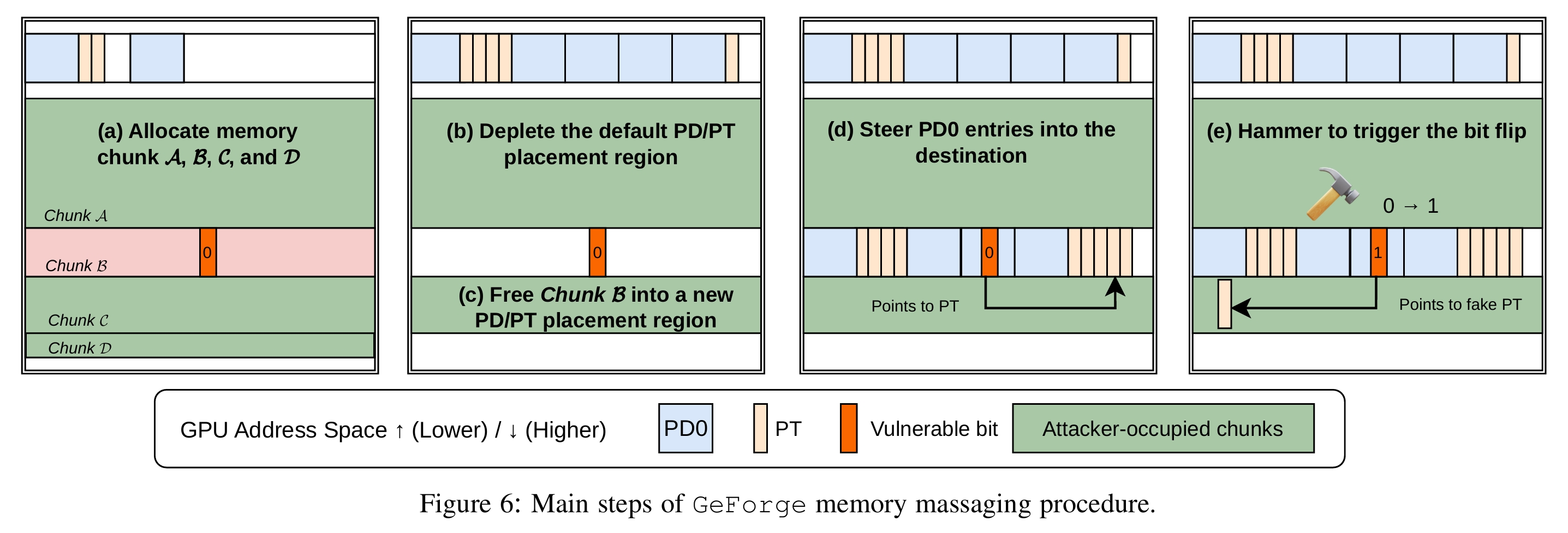
The team was able to induce 1,171 bit flips on an RTX 3060 and 202 bit flips on an RTX A6000. That obviously cripples the GPU's memory, but according to the research paper, it also means that "an attacker can modify the page table on the GPU to point to memory on the CPU, thereby giving the attacker the ability to read/write all of the CPU’s memory as well, which of course completely compromises the machine.”
So far, only GDDR6 memory seems to be affected by these Rowhammer attacks, and the team tested 25 GPUs with it, finding vulnerabilities in most. More modern cards with GDDR6X or GDDR7 memory were also tested, but couldn't be compromised yet. Nvidia has already suggested enabling ECC to mitigate against Rowhammer attacks, but that reduces total VRAM capacity, introduces performance overhead, and isn't available on every GPU.
The other option is to enable IOMMU (Input–Output Memory Management Unit) in the BIOS, which puts a strict boundary around non-CPU devices when they try to access system memory. Usually, a GPU can read or write system memory without requesting the CPU every time (Direct Memory Access), which is how GDDRHammer or GeForge slip into system RAM. But with IOMMU enabled, corrupted page tables with incorrect mapping couldn't be exploited to gain access to the CPU since they'd be cordoned off.
Think of it as putting the GPU in a sandbox where it can still talk to the CPU, but it's not allowed to go around it. Of course, if the IOMMU itself is misconfigured or targeted in an attack, it can be bypassed as well, but it is the best line of defense for now. The researchers themselves admit that enabling IOMMU closes the vulnerability. By default, it's kept disabled in the BIOS to avoid compatibility problems because it's so stringent.
Rowhammer attacks, while dangerous, still require the attacker to have access to your system in order to run code that will start the process. So, you're not as actively exposed compared to other remote attacks. However, in a network of shared computers, maybe a cluster of GPUs running AI workloads, the risk is increased, so it's important to stay vigilant and informed, nonetheless. Check out the linked research papers if you want to dive deep into the specifics of how either attack works.

Follow Tom's Hardware on Google News, or add us as a preferred source, to get our latest news, analysis, & reviews in your feeds.

 4 days ago
17
4 days ago
17






 English (US) ·
English (US) ·