Microsoft has confirmed that the April 2026 security updates are causing failures in third-party backup applications using the psmounterex.sys driver.
As BleepinComputer reported last week, this issue affects software using VSS (Volume Shadow Copy Service) snapshots and causes failures due to a VSS service timeout.
Software impacted by this includes, but is not limited to, products from Macrium (Reflect), Acronis (Cyber Protect Cloud), UrBackup Server, and NinjaOne Backup running on Windows 11, Windows Server, and Windows 10 devices.
Microsoft has now updated its support documents to confirm that the April updates include a security hardening change that adds psmounterex.sys to the company's vulnerable driver blocklist to defend users against attacks targeting a high-severity buffer overflow vulnerability (CVE-2023-43896) that allows attackers to escalate privileges or execute arbitrary code.
Microsoft also advised those affected by this issue to update to a newer version of their app that uses newer drivers, which include the required protections.
On impacted systems, where the vulnerable drive is blocked by Windows Code Integrity enforcement, IT admins and users may observe the following behavior:
- Backup applications that rely on the kernel driver psmounterex.sys might fail to mount backup image files as virtual drives.
- Attempting to browse or restore from a backup image might result in errors or timeouts.
- Failures might be followed by error messages, such as "The backup has failed because Microsoft VSS has timed out during the snapshot creation" or VSS_E_BAD_STATE.
- Event Viewer might show Code Integrity errors indicating that psmounterex.sys was blocked from loading.
- Backup creation (full image backups) may still succeed, but image-mount operations will fail.
"In the April 2026 Windows security update, we added known vulnerable kernel driver psmounterex.sys to the Vulnerable Driver Blocklist. Backup applications that rely on this driver may experience failures when attempting to mount or manage disk images," Microsoft told BleepingComputer.
"We do not recommend uninstalling or pausing this update. Customers with an impacted driver should install the latest application versions and validate against the driver blocklist to remain protected."
To check whether the Microsoft Vulnerable Driver Blocklist blocks a driver, affected customers can look for 'Event ID 3077' with Policy ID {D2BDA982-CCF6-4344-AC5B-0B44427B6816} in the Code Integrity Operational log, which indicates that the psmounterex driver was blocked in enforcement mode.
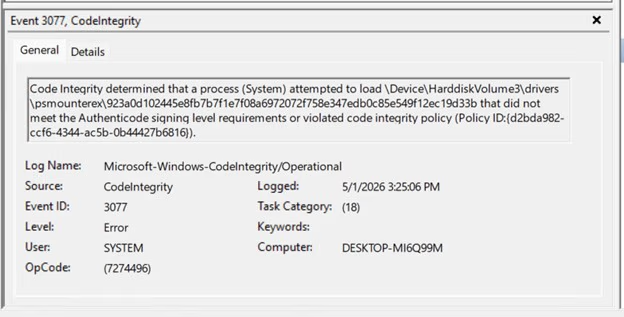 'Event 3077' entry in Event Viewer (Microsoft)
'Event 3077' entry in Event Viewer (Microsoft)To do that, right-click Start, select Event Viewer, go to 'Applications and Services Logs\Microsoft\Windows\CodeIntegrity\Operational' in the left pane, and look for Event ID 3077 in the middle pane.
Earlier this month, Microsoft warned that some Windows Server 2025 devices may also boot into BitLocker recovery mode, prompting users to enter the BitLocker key after installing the KB5082063 update.
Microsoft also released out-of-band (OOB) updates to fix issues affecting Windows Server systems that caused update installation failures and restart loops after installing the April 2026 security updates.
99% of What Mythos Found Is Still Unpatched.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what's exploitable, proves controls hold, and closes the remediation loop.









 English (US) ·
English (US) ·