Progress Software warned customers to patch a critical authentication bypass vulnerability in its MOVEit Automation enterprise-grade managed file transfer (MFT) application.
MOVEit Automation automates complex data workflows without requiring manual scripting and serves as a central automation orchestrator to schedule and manage file transfers between different systems, including local servers, cloud storage, and external partners.
Tracked as CVE-2026-4670, the security flaw affects MOVEit Automation versions before 2025.1.5, 2025.0.9, and 2024.1.8. Remote threat actors can exploit it without privileges on the targeted systems in low-complexity attacks that don't require user interaction.
"We have addressed the vulnerability and the Progress MOVEit Automation team strongly recommends performing an upgrade to the latest version," the company says in a Thursday advisory. "Upgrading to a patched release, using the full installer, is the only way to remediate this issue. There will be an outage to the system while the upgrade is running."
The same day, Progress also released security updates to address a high-severity privilege escalation vulnerability (CVE-2026-5174) stemming from an improper input validation weakness in the same software.
According to a Shodan search shared by PwnDefend cybersecurity consultant Daniel Card, over 1,400 MOVEit Automation instances are exposed online, and over a dozen are linked to U.S. local and state government agencies.
However, there is no information regarding how many of these systems have already been secured against CVE-2026-4670 attacks.
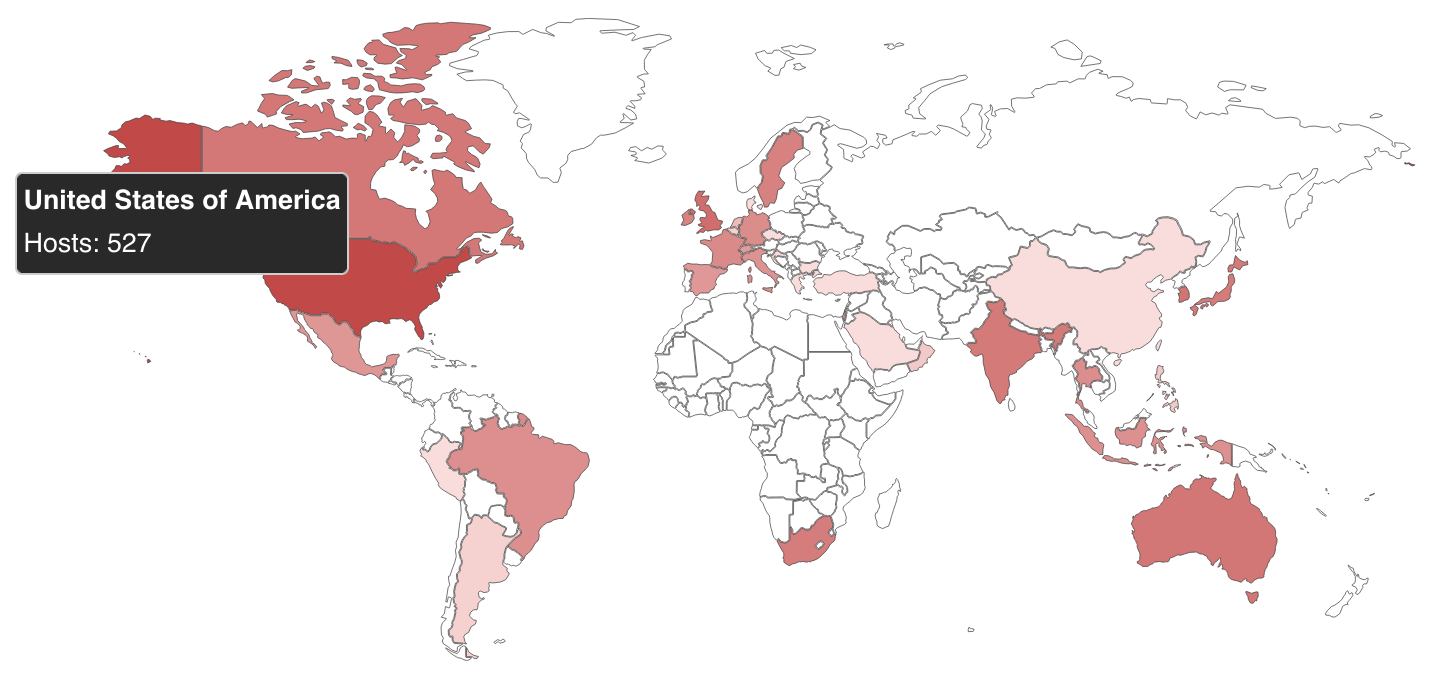 Map of MOVEit Automation instances exposed online (Shodan)
Map of MOVEit Automation instances exposed online (Shodan)While the company has yet to flag these security issues as exploited in the wild, other MoveIT MFT vulnerabilities have been targeted in attacks in recent years.
For instance, the Clop ransomware gang exploited a zero-day in the MOVEit Transfer secure file transfer platform in an extensive series of data theft attacks in 2023 that affected more than 2,100 organizations and over 62 million individuals, according to Emsisoft estimates.
MFT software is an attractive target for ransomware actors, as seen in previous Clop data-theft campaigns targeting security flaws in Accellion FTA, SolarWinds Serv-U, Gladinet CentreStack, GoAnywhere MFT, and Cleo.
Progress Software says its MOVEit MFT solutions are used by more than 3,000 enterprise organizations and over 100,000 users worldwide.
99% of What Mythos Found Is Still Unpatched.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what's exploitable, proves controls hold, and closes the remediation loop.







 English (US) ·
English (US) ·