- While modern encryption protects most logins, rogue Wi-Fi networks can still track your browsing or spoof unencrypted sites.
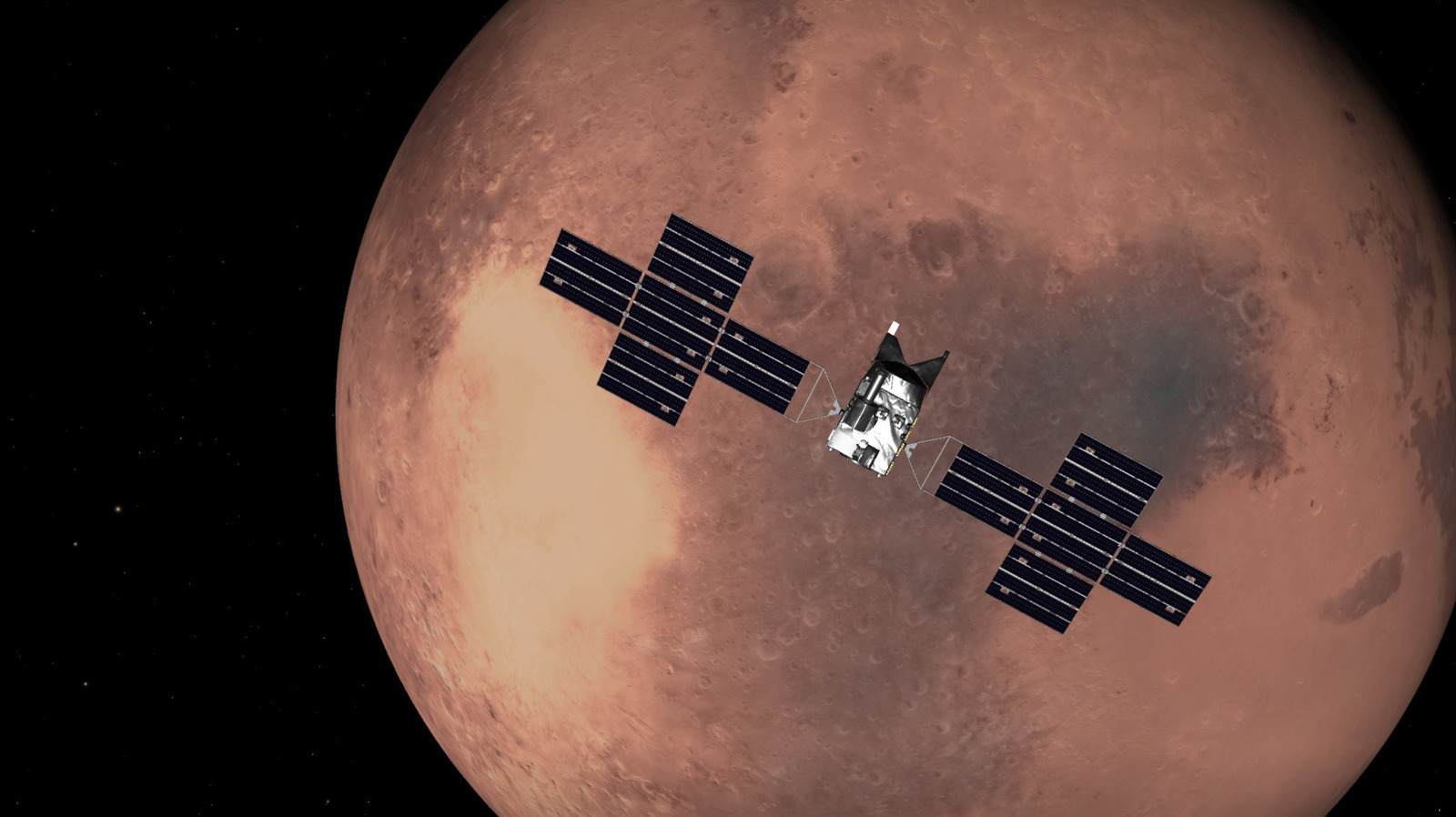
- A VPN routes your traffic through an encrypted tunnel, adding an extra layer of privacy on public connections
- Several VPN providers now offer bundled eSIMs, letting you bypass risky public Wi-Fi altogether
During busy summer travel season, airport departure lounges are packed with people looking for a quick internet connection. Whether you are checking for gate changes, sending a quick work email, or downloading entertainment for the flight, logging onto the free terminal Wi-Fi is an automatic habit for most travelers.
However, open public networks lack the security of your home or office connection, introducing potential privacy risks.
While your banking apps and major websites use encryption to shield your absolute most sensitive information, using unencrypted open networks can still expose your browsing habits, local network traffic, and personal details to third-party tracking.
The biggest threat to your data isn't the airport's official network; it is the ones pretending to be. Hackers can set up rogue hotspots, a tactic known as an ‘Evil Twin’ attack.
They broadcast network names like "Airport_Free_WiFi_5G", which look entirely official. However, if you connect to one of these networks, unencrypted traffic could potentially be monitored by whoever is running the hotspot.
On a legitimate airport network, sophisticated Man-in-the-Middle (MITM) attacks can theoretically allow an attacker to intercept data between your device and the router.
Fortunately, because nearly all major websites and financial apps now use HTTPS encryption, passwords and credit card data remain heavily protected even if that data is intercepted.
A more practical concern is the standard airport "captive portal" — the login screen where you accept terms or watch an ad. Many of these pages remain unencrypted, meaning any email address, phone number, or travel details you enter to get online could potentially be visible to others on the open network.
The one tool you need
For those who frequently rely on public networks, a virtual private network (VPN) offers an extra layer of privacy.
When you switch on a VPN, it creates a secure, encrypted tunnel between your device and the internet. This ensures that even if you accidentally connect to a rogue "Evil Twin" hotspot, or if someone is monitoring the local airport network, your browsing activity and data look like scrambled, unreadable code to outside observers.
It is also worth checking if a VPN provider includes a Kill Switch, a highly useful feature when traveling. Because airport Wi-Fi is notoriously unstable, connections frequently drop and reconnect. A Kill Switch automatically pauses your device’s internet access the moment a connection dips, preventing your smartphone or laptop from reverting to an open, unencrypted broadcast before the VPN has time to re-establish its secure tunnel.
The all-in-one solution: VPN and eSIMs
Alternatively, the most straightforward way to avoid public network vulnerabilities is to bypass them entirely using mobile data.
With the rise of digital eSIM cards, travelers can now download local data plans before they even depart.
Several major security firms have recently integrated these services. For example, Nord Security launched a standalone eSIM app called Saily, while ExpressVPN introduced tiers that include limited travel data. Other standalone eSIM options like Airalo or Holafly offer similar ways to bypass public networks.
This means you can switch directly to local 5G or LTE networks the moment the plane lands, ensuring a reliable connection without ever having to engage with an airport portal page.





 English (US) ·
English (US) ·