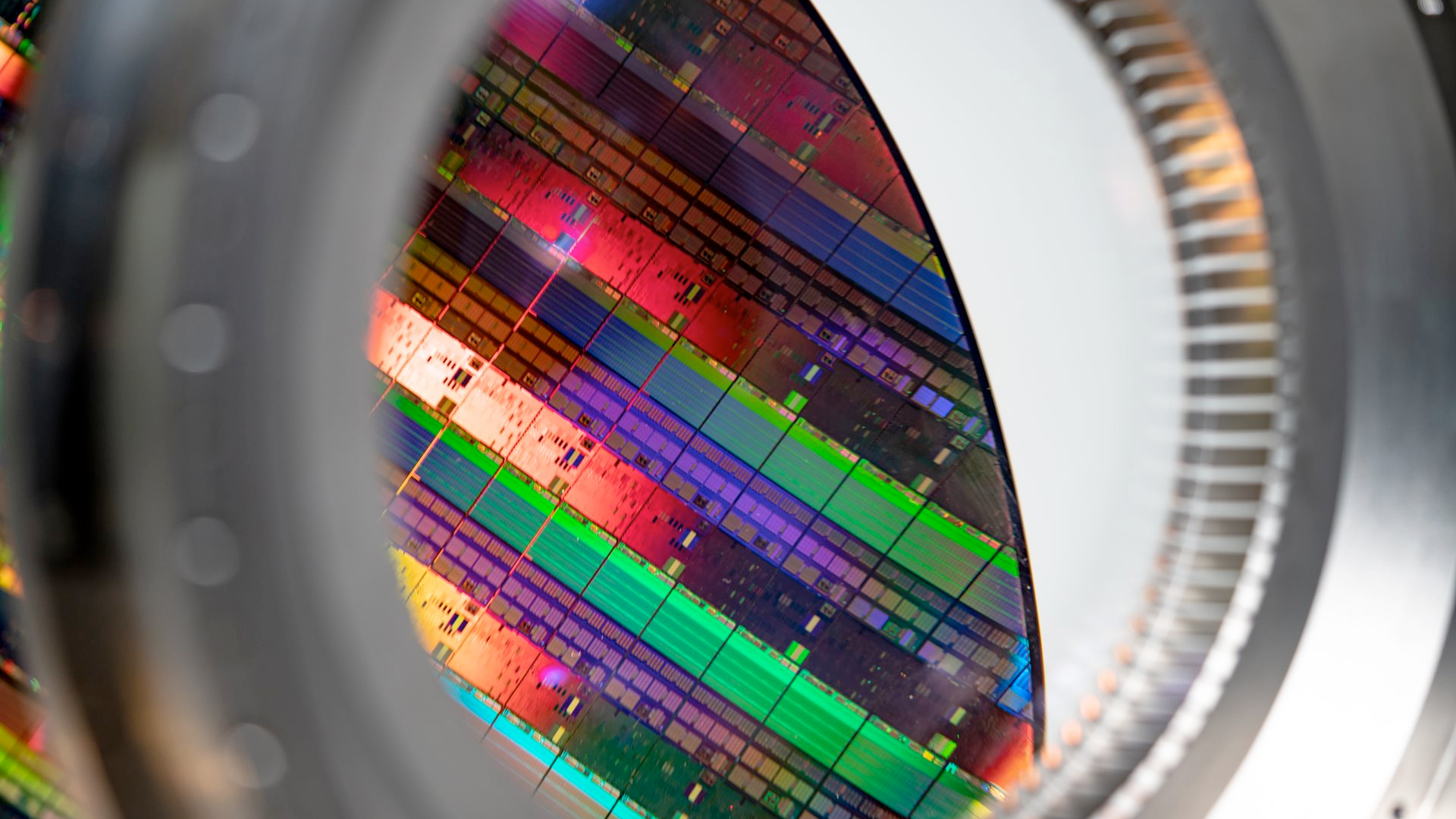
Researchers at Adelaide University have made a discovery that could change the way we test semiconductors for good. As reported by IEEE Spectrum, these researchers have discovered a method of detecting a chip's transistor activity using terahertz radiation.
Go deeper with TH Premium: Chipmaking
Testing requires the chip to be turned on and to be doing work. As the transistors inside switch on and off, the terahertz signal reflects these changes and returns to a receiver in the VNA extender. Afterward, the signal is "down-converted" to microwave and compared to the original signal by detecting tiny differences in amplitude and phase using a homodyne quadrature receiver.
Article continues below
One of the researchers, Withawat Withayachumnankul, revealed his team had to hack the receiver to make it work in the terahertz domain. The device was only designed to compare microwave frequencies. The use of a homodyne detector was critical, as it is allegedly the only device that can detect the small differences between the two frequencies. Terahertz signals are physically larger than the transistors being probed by the signal, making any adjustments in the returning signal difficult to detect without a homodyne detector. Additionally, noise from the oscillator in the VNA can reportedly easily obscure any changes in signal difference as well.
The most intriguing part of this new technology is its ability to peer into a processor's internals while it is working. This is something that is reportedly not possible with any other tooling and opens up new possibilities for technicians to diagnose and test processors.
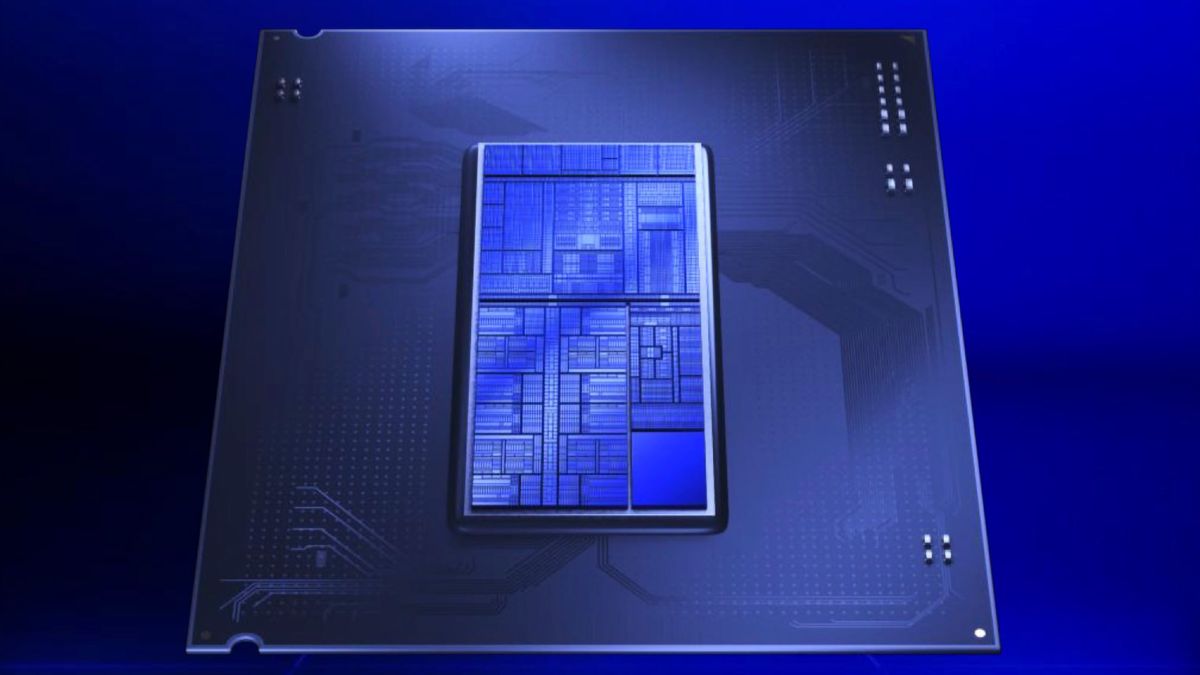
However, there are issues that need to be ironed out before this technology goes mainstream. Measuring CPUs with terahertz radiation can reportedly be problematic with complex chips that have multitudes of layers of components stacked on top of one another, such as CPUs equipped with 3D stacked chiplets, potentially. Specifically, the radiation can't detect which layer of a chip it is reading from if the "over-layers are opaque". To get around this, techniques are being discussed to increase the VNA's sensitivity to accurately test densely packed chips.
Another issue with this technology is the potential for attackers to probe into a CPU as it is running to steal data. Likely, this will only happen once the technology matures, but it is something that the security industry will likely need to start countermeasuring eventually. What makes this attack so dangerous is that outgoing encryption standards can't counter it, since CPUs have to decrypt data before processing it.
Follow Tom's Hardware on Google News, or add us as a preferred source, to get our latest news, analysis, & reviews in your feeds.


 2 hours ago
7
2 hours ago
7





 English (US) ·
English (US) ·