
A fake version for the Claude AI website offers a malicious Claude-Pro Relay download that pushes a previously undocumented backdoor for Windows named Beagle.
The threat actor advertises Claude-Pro as a "high-performance relay service designed specifically for Claude-Code" developers.
The fake website is a simplistic attempt at mimicking the legitimate site for the popular Claude large language model (LLM) and an AI assistant, using similar colors and fonts.
However, the facade falls apart when it comes to links, as they are mere redirects to the front page, researchers at cybersecurity company Sophos say in a report today.
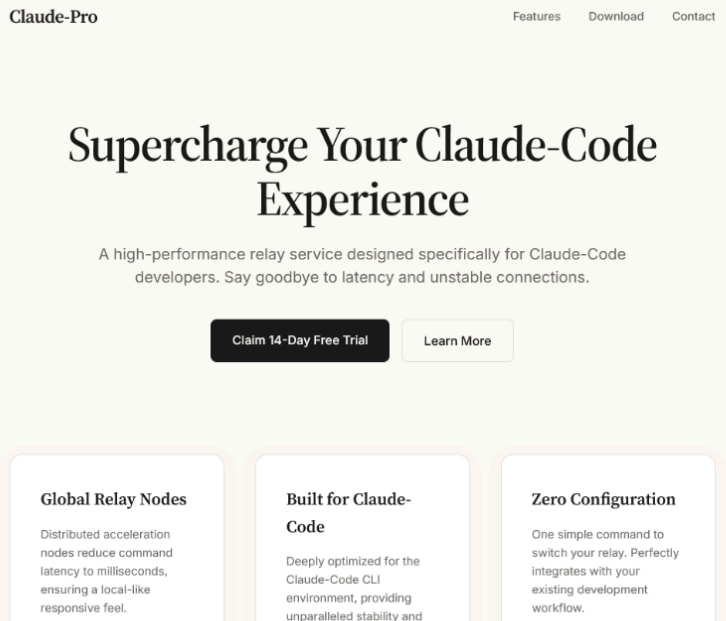 Fake Claude AI website
Fake Claude AI websiteSource: Sophos
Users landing on “claude-pro[.]com” that fail to see through the deception can only click on a large download button for the malicious resource, a 505MB archive named 'Claude-Pro-windows-x64.zip' that contains an MSI installer allegedly for the Claude-Pro Relay product.
Sophos says that running the binary leads to adding three files to the Startup folder: NOVupdate.exe, NOVupdate.exe.dat, and avk.dll.
The campaign was initially discovered by Malwarebytes, whose researchers say that the 'Pro' installer is a trojanized copy of Claude that works as expected but deploys a PlugX malware chain in the background, giving attackers remote access to the system.
Looking closer at the campaign, Sophos discovered that the first-stage payload was DonutLoader that fetched "a relatively simple backdoor" the researchers call Beagle, with a limited set of commands:
- uninstall: uninstalls agent
- cmd: executes command
- upload: uploads file
- download: downloads file
- mkdir: creates directory
- rename: renames file
- ls: lists directory content
- rm: removes directory
It is worth clarifying that the Beagle backdoor is distinct from the Delphi-based Beagle/Bagle worm documented in 2004.
According to the researchers, NOVupdate.exe is a signed updater for G Data security solutions that the hacker uses to sideload the malicious avk.dll and the encrypted NOVupdate.exe.dat file.
Sophos notes that sideloading the AVK DLL and an encrypted file using a G Data signed executable have been linked to PlugX activity in the past.
The role of the DLL is to decrypt and execute in memory the payload inside NOVupdate.exe.dat, which is the open-source in-memory injector DonutLoader. Sophos spotted Donut before, in attacks in 2024 that targeted government organizations in Southeast Asia.
In this case, Donut deploys the final payload, the Beagle backdoor, into the system memory to evade detection.
The backdoor communicates with the command-and-control (C2) at ‘license[.]claude-pro[.]com’ using TCP over port 443 and/or UDP over port 8080, while a hardcoded AES key protects the exchanges.
Sophos note that the C2 is hosted at 8.217.190[.]58, an IP address that Malwarebytes researchers say is in the range associated with the Alibaba-Cloud service.
Further investigation led Sophos to additional samples related to Beagle, which were submitted to VirusTotal between February and April this year, and using the same XOR decryption key for decryption.
However, those samples infected machines via different attack chains, including Microsoft Defender binaries, AdaptixC2 shellcode and a decoy PDF, and impersonating update sites from multiple security vendors (e.g., CrowdStrike, SentinelOne, and Trellix).
Although Sophos was unable to confidently attribute the campaign to a threat actor, the researchers suggest that the same operators behind PlugX might be experimenting with a new payload.
To mitigate this risk, users should ensure they are downloading Claude from the official portal and skip or hide sponsored search results. The presence of ‘NOVupdate’ files on a system is a strong indication of compromise.
99% of What Mythos Found Is Still Unpatched.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what's exploitable, proves controls hold, and closes the remediation loop.









 English (US) ·
English (US) ·